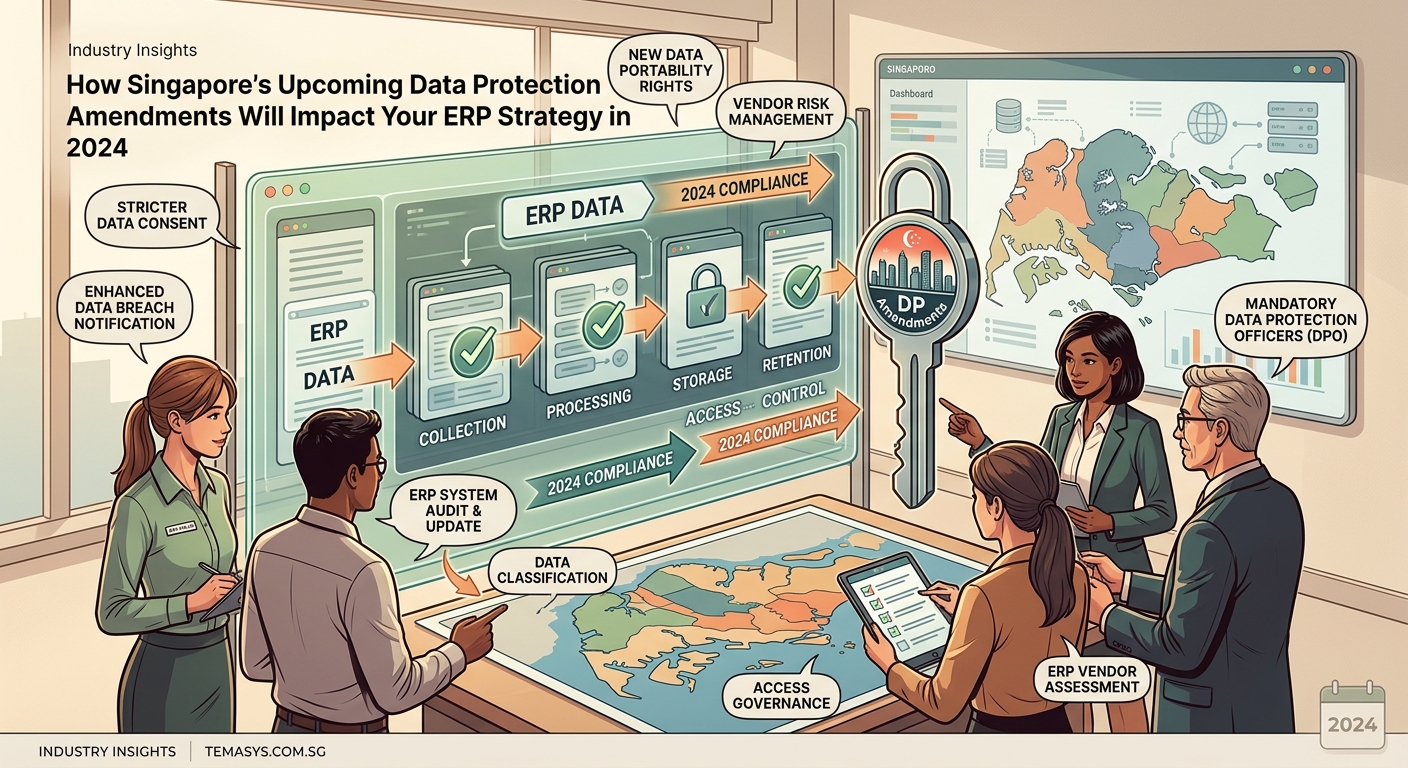
The Personal Data Protection Act amendments rolling out across 2025 represent the most significant regulatory shift in Singapore’s data governance landscape since the original legislation took effect in 2013. For organisations running enterprise resource planning systems, these changes aren’t just legal footnotes. They’re operational imperatives that will reshape how you collect, store, process, and transfer customer and employee data.
Singapore’s data protection amendments 2024 introduce mandatory data breach notifications, expanded definitions of sensitive personal data including biometric information, direct obligations for data processors, increased penalties reaching S$1 million, and new data portability rights. These changes require immediate ERP system audits and configuration updates to maintain compliance throughout the three-phase implementation schedule.
Understanding the three-phase rollout schedule
The amendments take effect in stages, giving organisations time to adapt their systems and processes.
Phase one began on 1 January 2025 with administrative changes that don’t impose new obligations but clarify existing requirements. Think of this as the warm-up period.
Phase two launched on 1 April 2025 and brought the substantial changes. The term “data user” is now “data controller.” Sensitive personal data now explicitly includes biometric data like fingerprints and facial recognition patterns. Data processors face direct regulation under security principles. Maximum penalties jumped to S$1 million or 10% of annual turnover for organisations, whichever is higher. Individual officers can face up to three years imprisonment.
Phase three takes effect on 1 June 2025 with mandatory data protection officer appointments, breach notification requirements, and data portability rights.
Your ERP system needs to accommodate all three phases, not just the current one.
What counts as sensitive personal data now

The expanded definition matters because sensitive data requires heightened protection measures.
Previously, the PDPA didn’t explicitly define sensitive personal data, leaving organisations to interpret requirements. The amendments remove that ambiguity.
Sensitive personal data now includes:
- Biometric data used for identification
- Health information
- Financial information
- Race or ethnicity
- Religious or philosophical beliefs
- Sexual orientation
- Political opinions
- Trade union membership
If your ERP system processes employee attendance through fingerprint scanners, that’s biometric data requiring enhanced security. Customer facial recognition for retail authentication falls under the same category. Medical leave records, insurance claims, payroll data linked to religious holidays, all of these trigger additional obligations.
Many Singapore organisations discovered their ERP systems were already processing sensitive data without appropriate controls. The amendments simply made the requirements explicit and enforceable.
Data processor obligations you can’t ignore
This represents a fundamental shift in responsibility allocation.
Previously, data processors operating on behalf of data controllers faced indirect obligations. If you hired a payroll service provider or cloud hosting company, they weren’t directly liable under the PDPA. The data controller bore the responsibility.
The amendments change that completely. Data processors now face direct obligations under the security principle. They must implement reasonable security arrangements to protect personal data. They can be investigated, sanctioned, and penalised independently of the data controller.
For ERP systems, this matters because most modern implementations involve multiple data processors. Your cloud infrastructure provider, your ERP vendor providing managed services, your backup and disaster recovery provider, your system integrator maintaining the platform, all of these entities are now directly regulated.
“The direct regulation of data processors eliminates the compliance gap that existed when third parties handled personal data without direct PDPA obligations. Organisations can no longer assume their vendors will maintain appropriate security just because the contract requires it. Vendors face independent legal liability now.”
You need to audit every data processor touching your ERP system. Verify they understand their obligations. Confirm they’ve implemented appropriate security measures. Update contracts to reflect the new regulatory landscape.
Mandatory data protection officer requirements

Not every organisation needs to appoint a DPO, but the thresholds are lower than many expect.
You must appoint a data protection officer if your organisation meets any of these criteria:
- Processing personal data involving more than 20,000 data subjects
- Processing sensitive financial information for more than 10,000 data subjects
- Conducting activities requiring regular and systematic monitoring of personal data
The “data subjects” count isn’t your employee headcount. It’s the number of individuals whose data you process. For most businesses, this includes employees, customers, suppliers, contractors, and anyone else in your systems.
A retail business with 50 employees but 25,000 customers in their ERP system needs a DPO. A logistics company tracking delivery recipients across multiple clients likely exceeds the threshold. A property management firm maintaining tenant records almost certainly qualifies.
The DPO can be an existing employee taking on additional responsibilities or an outsourced service provider. The role can be part-time or full-time, depending on your organisation’s needs.
Your DPO doesn’t need to be a lawyer, but they need sufficient authority and resources to monitor compliance effectively. Burying the role three levels down in the IT department won’t satisfy the requirement.
Data breach notification timelines and triggers
The mandatory breach notification requirement introduces strict timelines that many organisations aren’t prepared to meet.
When a personal data breach occurs, data controllers must assess whether it’s likely to result in significant harm to affected individuals. If yes, you must notify both the Personal Data Protection Commission and the affected individuals.
The notification to the PDPC must happen “as soon as practicable,” which regulatory guidance interprets as within 72 hours of becoming aware of the breach. Notifications to individuals should happen without undue delay.
“Significant harm” isn’t defined exhaustively, but includes:
- Identity theft or fraud
- Financial loss
- Damage to reputation
- Physical harm
- Psychological harm
- Loss of employment or business opportunities
Your ERP system needs mechanisms to detect potential breaches, assess their severity, identify affected individuals, and facilitate notifications within the required timeframes. Most legacy systems weren’t designed with these capabilities.
Consider a scenario where an employee accidentally emails a customer database extract to the wrong recipient. You need to know this happened, determine how many individuals are affected, assess the risk of harm, and potentially notify thousands of people within 72 hours. Without automated detection and response workflows, you won’t meet the deadline.
| Breach Type | Detection Method | Notification Required | Timeline |
|---|---|---|---|
| Unauthorised access to employee payroll | System access logs, anomaly detection | Yes, if financial data exposed | Within 72 hours to PDPC |
| Accidental email to wrong recipient | Email gateway monitoring, user reports | Depends on data sensitivity | Assess immediately |
| Ransomware encryption of customer database | Endpoint protection, backup monitoring | Yes, if data exfiltrated | Within 72 hours to PDPC |
| Lost laptop with unencrypted HR records | Asset management, user reporting | Yes, device contains sensitive data | Within 72 hours to PDPC |
| Database misconfiguration exposing records | Vulnerability scanning, penetration testing | Yes, if publicly accessible | Within 72 hours to PDPC |
Data portability rights and ERP system capabilities

Starting 1 June 2025, individuals can request their personal data in a commonly used, machine-readable format and ask you to transmit it directly to another data controller.
This mirrors the GDPR’s data portability right but with Singapore-specific implementation details.
For ERP systems, this creates technical challenges. Your system needs to:
- Identify all personal data belonging to a specific individual across multiple modules
- Extract that data in a structured format
- Present it in a commonly used, machine-readable format like CSV, JSON, or XML
- Potentially transmit it directly to another organisation’s system
Most ERP implementations store personal data across dozens of tables and modules. An employee’s information might span HR, payroll, benefits, time tracking, expense management, and project allocation modules. A customer’s data could exist in sales, service, billing, shipping, and marketing modules.
Manually compiling this information for each portability request isn’t sustainable. You need automated extraction capabilities built into your ERP system or implemented through middleware.
The “technical feasibility” exception provides some relief. You don’t need to transmit data if it’s not technically feasible or if the receiving system can’t accept it. But you still need to provide the data to the individual in a portable format.
Cross-border data transfer requirements
The amendments modify how organisations can transfer personal data outside Singapore.
Previously, you could transfer personal data overseas if the receiving jurisdiction provided a standard of protection comparable to Singapore’s PDPA. The amendments clarify and expand these provisions.
You can now transfer personal data to countries with substantially similar data protection laws or equivalent levels of protection. The Personal Data Protection Commission maintains a list of jurisdictions meeting this standard, though the list remains limited.
For transfers to other jurisdictions, you need to ensure the receiving organisation provides a comparable standard of protection through contractual obligations, binding corporate rules, or other mechanisms.
Many Singapore organisations operate regional ERP systems hosted in data centres outside Singapore. A manufacturing company might run SAP in Malaysia. A logistics firm might use Oracle Cloud hosted in Australia. A retail chain might process transactions through systems in Hong Kong.
Each of these scenarios involves cross-border data transfers requiring compliance with the amended requirements. Your cloud ERP vs on-premise deployment decision now carries regulatory implications beyond technical and financial considerations.
Conducting an ERP compliance audit
You can’t fix what you don’t measure. Start with a comprehensive audit of your current state.
- Map all personal data flows through your ERP system, including collection points, storage locations, processing activities, and transfer destinations.
- Identify which data qualifies as sensitive under the expanded definition, paying particular attention to biometric data, health information, and financial records.
- Document all data processors with access to your ERP system, including cloud providers, managed service vendors, system integrators, and backup services.
- Review your current security controls against the enhanced requirements for sensitive data protection.
- Assess your breach detection and response capabilities against the 72-hour notification timeline.
- Evaluate your data extraction capabilities for portability requests.
- Examine cross-border data transfers and verify appropriate safeguards are in place.
The audit will reveal gaps between your current configuration and compliance requirements. Prioritise gaps based on regulatory deadlines and risk exposure.
A mid-sized distributor conducting this audit discovered they were processing biometric attendance data for 300 employees without enhanced security controls. Their ERP system stored this data in the same database as general HR information, with identical access permissions. They had 45 days to implement segregated storage, enhanced encryption, and restricted access before the phase two deadline.
Configuring ERP systems for compliance
Technical implementation varies by platform, but certain patterns apply across most enterprise systems.
Implement role-based access controls that restrict sensitive data access to authorised personnel only. Your payroll manager doesn’t need access to employee medical records. Your sales team doesn’t need to see customer financial information beyond what’s necessary for their role.
Enable comprehensive audit logging for all access to sensitive personal data. You need to know who accessed what data, when they accessed it, what they did with it, and whether the access was authorised. These logs become essential for breach detection and investigation.
Configure data retention policies that automatically purge personal data when it’s no longer needed for the original collection purpose. Many ERP systems retain data indefinitely by default. The amendments require you to establish and enforce retention periods.
Implement data masking for non-production environments. Your testing and development systems shouldn’t contain real personal data. Use anonymisation or pseudonymisation techniques to create realistic test data without exposing actual individuals’ information.
Set up automated breach detection mechanisms. This might involve anomaly detection for unusual data access patterns, integration with security information and event management systems, or scheduled vulnerability assessments.
Build data portability workflows that can extract an individual’s complete data set across all ERP modules. This likely requires custom development or third-party tools, as most ERP platforms don’t provide this functionality out of the box.
Vendor and contract management updates
Your ERP vendor relationships need updating to reflect the new regulatory environment.
Review your software licensing agreements, cloud service contracts, implementation agreements, and managed services contracts. Look for provisions addressing data processor obligations, breach notification procedures, data localisation requirements, and liability allocation.
Most contracts signed before the amendments don’t adequately address the new requirements. Your cloud provider’s standard terms probably don’t commit to 72-hour breach notifications. Your managed services agreement likely doesn’t specify the security controls required for sensitive data processing.
Negotiate amendments or addenda that explicitly address:
- The vendor’s role as a data processor and their direct PDPA obligations
- Security measures for protecting sensitive personal data
- Breach detection and notification procedures, including timelines
- Data localisation or cross-border transfer safeguards
- Audit rights allowing you to verify compliance
- Liability and indemnification for regulatory violations
Don’t assume your ERP vendor selection process from three years ago considered these regulatory requirements. The landscape has changed fundamentally.
Training and awareness programmes
Technology changes are necessary but not sufficient. Your people need to understand their obligations.
Data protection training shouldn’t be a one-time compliance exercise. It needs to be ongoing, role-specific, and practical.
Your IT team needs technical training on security controls, breach detection, and incident response. Your HR team needs guidance on processing sensitive employee data. Your sales team needs to understand customer data collection and consent requirements. Your executives need awareness of their personal liability under the enhanced penalty provisions.
Scenario-based training works better than policy documents. Present realistic situations your staff might encounter:
- An employee receives a phone call from someone claiming to be from HR requesting employee personal data
- A customer emails asking for all their data to be transferred to a competitor
- A laptop containing customer information goes missing
- A vendor requests access to production data for troubleshooting
- An employee notices unusual database queries in system logs
Walk through the correct response for each scenario. Make it clear what actions are required, who needs to be notified, and what the consequences of incorrect handling might be.
Balancing compliance with operational efficiency
Compliance requirements can feel like obstacles to business operations. The key is finding implementations that satisfy regulatory obligations without creating unnecessary friction.
A logistics company needed to implement enhanced security for customer financial data in their ERP system. The obvious solution was requiring multi-factor authentication for every access. But their warehouse staff accessed the system hundreds of times per shift for order processing. Constant authentication prompts would have destroyed productivity.
They implemented a risk-based approach instead. Standard order information remained easily accessible. Financial data triggered additional authentication only when accessed, which happened infrequently for most users. High-risk activities like bulk data exports required additional approval workflows.
The solution satisfied compliance requirements while maintaining operational efficiency for 95% of system interactions.
Look for similar opportunities in your implementation. Not every control needs to apply to every user or every transaction. Risk-based approaches, contextual security, and intelligent automation can achieve compliance without grinding operations to a halt.
Cost implications and budget planning
Compliance isn’t free. You need realistic budget estimates for the changes required.
Technical implementations typically involve:
- Software licensing for enhanced security tools, encryption solutions, or data discovery platforms
- Professional services for system configuration, custom development, or integration work
- Infrastructure upgrades for additional storage, processing capacity, or redundancy
- Ongoing maintenance and support for new capabilities
A mid-sized manufacturer budgeted S$45,000 for their ERP compliance project, covering:
- S$12,000 for data discovery and classification tools
- S$18,000 for security enhancements including encryption and access controls
- S$8,000 for breach detection and response workflows
- S$7,000 for training and awareness programmes
These figures don’t include the internal staff time required for project management, testing, and change management. Factor in 200 to 400 hours of internal effort for a typical mid-sized implementation.
Larger organisations with complex ERP landscapes can expect costs in the S$150,000 to S$500,000 range, depending on the number of systems, data volumes, and integration complexity.
The cost of non-compliance provides perspective. A single breach notification incident can cost S$50,000 to S$200,000 in investigation, notification, remediation, and regulatory response. Penalties for non-compliance reach S$1 million. Reputational damage is harder to quantify but potentially more costly.
Building a business case for these investments requires framing compliance as risk mitigation rather than pure cost.
Industry-specific considerations
Different sectors face unique challenges with the amendments.
Healthcare organisations already handle sensitive health information, but the amendments expand biometric data requirements. Patient identification systems using fingerprints or facial recognition need enhanced security. Medical records systems require stricter access controls. Data portability requests become complex when medical data spans multiple systems and providers.
Financial services firms process extensive sensitive financial information. The 10,000 data subject threshold for mandatory DPO appointment applies to most banks, insurance companies, and investment firms. Cross-border data transfers for regional operations require careful attention. Breach notification obligations carry heightened reputational risks in a sector where trust is paramount.
Retail and hospitality businesses often underestimate their data processing volumes. A chain with 20 outlets and modest daily traffic easily exceeds 20,000 customers annually. Loyalty programmes, online ordering systems, and customer service platforms all process personal data requiring protection. Biometric payment authentication systems trigger sensitive data requirements.
Manufacturing and logistics companies process employee biometric data through attendance systems, customer information through order management, and supplier data through procurement systems. Industry-specific ERP solutions need configuration for sector-specific compliance requirements.
Common implementation mistakes to avoid
Learning from others’ errors saves time and money.
Treating compliance as an IT project alone. Data protection is a business issue requiring input from legal, HR, operations, and executive leadership. IT implements the technical controls, but business stakeholders define the requirements and own the outcomes.
Focusing only on customer data. Employee data often presents greater compliance challenges. HR systems process sensitive health information, financial data, and increasingly biometric data. Employee portability requests can be more complex than customer requests because the data spans more systems.
Underestimating data discovery complexity. You can’t protect data you don’t know exists. Many organisations discover personal data in unexpected places during compliance audits. That old SharePoint site with employee records. The archived database from a discontinued system. The spreadsheets users created for one-off projects.
Implementing controls that users bypass. Security measures that create excessive friction encourage workarounds. Users start emailing sensitive data to personal accounts to avoid access restrictions. They write down complex passwords. They share credentials to avoid authentication delays. Design controls that balance security with usability.
Delaying until deadlines approach. The phase three deadline of 1 June 2025 is closer than it appears. Complex ERP implementations require months of planning, development, testing, and rollout. Starting in April means rushing and cutting corners.
Preparing for ongoing regulatory evolution
The amendments represent the current state, not the final destination. Singapore’s regulatory framework will continue evolving.
The Personal Data Protection Commission regularly issues guidance, advisory guidelines, and clarifications. Subscribe to their updates. Attend industry briefings. Join professional associations focused on data protection.
Build flexibility into your ERP systems. Hard-coded compliance rules become technical debt when regulations change. Configurable workflows, parameterised security controls, and modular architectures make future adjustments easier.
Establish a compliance review cadence. Quarterly reviews of your data protection posture, vendor compliance, incident trends, and regulatory developments keep you ahead of requirements rather than constantly catching up.
Monitor international developments. Singapore’s data protection regime draws inspiration from GDPR, APEC Privacy Framework, and other international standards. Changes in these frameworks often presage similar updates locally.
Moving forward with confidence
The Singapore data protection amendments 2024 create real obligations with meaningful consequences. But they also provide clarity. You know what’s required. You know when it’s required. You have the tools and knowledge to achieve compliance.
Start with the audit. Understand your current state. Identify the gaps. Prioritise based on deadlines and risk. Build a realistic implementation plan with appropriate budget and resources. Engage your vendors. Train your people. Test your capabilities. Document your decisions.
The organisations that treat this as a strategic opportunity rather than a compliance burden will emerge stronger. Better data governance improves operational efficiency. Enhanced security reduces breach risk. Clear policies simplify decision-making. Documented processes enable scaling.
Your ERP system is the operational backbone of your organisation. Making it compliant with Singapore’s data protection amendments 2024 isn’t just about avoiding penalties. It’s about building a foundation for sustainable, trusted, and efficient operations in an increasingly regulated environment.
The work starts now, but the benefits extend far beyond the compliance deadlines.